RETROGRADE IS SECURITY

THE INVISIBLE PRISON (PHYSICAL ENFORCEMENT)
When the algorithm flags you, the physical world closes in. This is no longer a localized threat; it is an active, cross-indexed reality. According to Flock Safety's CEO, their AI cameras now "cover almost 70 percent of the population." These little black boxes on utility poles aren't just looking for stolen sedans; they are the eyes of an integration engine that fingerprints your vehicle and maps your associations through Palantir.
The recent Super Bowl LX advertisement for Ring cameras reveals the dystopian reality; the practical gamification of informant culture. By framing mass AI surveillance as a “pet finder” feature, they have attempted to incentivize your neighbors to populate a national biometric database under the guise of communal care.
Involuntary Geolocation Amazon markets this "Neighbor-to-Neighbor" (N2N) protocol as a benefit, but its technical foundation, Amazon Sidewalk, creates a passive scanning grid. Operating on 900 MHz LoRa and Bluetooth Low Energy (BLE), it acts as a "Sidewalk Bridge"—a neighborhood mesh that communicates with devices that have no Wi-Fi credentials.

The argument from Amazon is that the network is encrypted to protect "Pet Finding." The reality is that Metadata is the Message. Even if your GrapheneOS device is in "Airplane Mode," if Bluetooth/Wi-Fi scanning is active, your device broadcasts a UUID. A neighbor’s Echo or Ring, acting as a "Sidewalk Gateway," picks up this ping and relays the timestamp and location to the cloud. You cannot "Opt-Out" of your neighbor's device indexing you on a public sidewalk.
As seen during the January 2026 Minneapolis protests, this mesh functions as a citizen-funded surveillance state where federal agencies can query metadata to track movement across entire ZIP codes.
The data reveals a darker application. A February 10, 2026, investigation by The Guardian exposed that ICE has been quietly leveraging these same school-district Flock cameras to target immigrant families during school drop-offs and pick-ups. The “safety” they sold to parents is now the trap that disenfranchises them.
The False Positive
The state markets these as surgical instruments, but the record proves they are blunt objects. 404 Media reported that ICE’s facial recognition misidentified the same woman twice. In the Palantir ecosystem, a bad scan is ingested as fact and becomes a permanent node in your metrics.
The Conscience of the Code
Listen to the architects. Following the January 2026 killing of Alex Pretti in Minneapolis, leaked internal Slack logs from Palantir Technologies leaked to Wired revealed employees in open revolt. When an employee asked if they built the database used to target critics, the executive response was a chilling evasion: "Palantir does not police the use of our platform for every workflow."
Translation: They built the gun, sold it to the highest bidder, and took no responsibility for the aim. The time for "trusting the system" has expired. For the deep dive behind these protocols, read my report:Future Crime Pipelines.
PART I: POCKET INFORMANTS (Cellphones)

Your choice of phone dictates your ceiling of freedom. There are only two viable paths.
Option A: The Sovereign Choice (GrapheneOS)
If you own a Google Pixel, you are obligated on principle, to install GrapheneOS. It is the only mobile OS that mathematically guarantees privacy by de-Googling the hardware.
- The Myth: “It breaks everything.”
- The Reality: I can personally confirm that Chase, Capital One, and Netflix work fine.
- The Protocol: You must use User Profiles. Keep your personal life (Signal, Notes, Photos) in the Main Profile. Create a Secondary Profile exclusively for “Hostile Apps” (Google Play Services, Banking, Uber). When you switch back to Main, those apps are frozen in a digital cryo-chamber, unable to track you.
Option B: The Feudal Lord (Apple)
Apple doesn't sell your data; they hoard it. They are part of the PRISM program and In 2021, announced plans to scan photos on your device for “illegal content” (CSAM), prior to uploading them to iCloud.
While a noble ideal, they paused the program after massive backlash, having proved that they have the capability and the willingness to target your private files at will.
If you choose to remain on their ecosystem, you have one defense: You MUST enable Advanced Data Protection (ADP).
- Without ADP: Apple holds the encryption keys to your iCloud backup and will hand them over to law enforcement.
- With ADP: The keys are deleted from Apple's servers. You alone hold the access.
For instructions on enabling ADP on your iPhone, check out this well written guide by Wired.
The Hierarchy of Trust:
- GrapheneOS: Trust No One. (Open Source, Verifiable).
- Apple (w/ ADP): Trust One Corporation. (Closed Source, Tim Cook's Pinky Promise).
- Stock Android: Trust the Ad Company. (You are the product).
To understand why I consider all stock android phones compromised, please refer to my write-up on the tech infrastructure mutating in the name of NSPM-7.
Part 1.5: CHANGING HOW YOU CONNECT (PC and Mobile)

Change your App Store
If you're running any version of android (stock or GrapheneOS), we've gotta change where you shop.
Google Play Store is like Walmart; its massive, convenient, and full of tracking cameras. Then theres F-Droid; this is your local Farmers Market.
What is it? F-Droid is an alternative app store for Android. It only hosts FOSS (Free and Open Source Software); not only free to use, you own the code.
- Open: The recipe is public. Anyone can check the code to ensure there is no hidden spyware.
- Safe: F-Droid builds the apps from the source code themselves. They don't just trust the developer; they verify the goods.
Why use it? Most apps in the Play Store exist to sell you, and your metrics. Apps on F-Droid exist to serve you. There are no “In-App Purchases”, no “Rate Me” pop-ups, and generally, no tracking.
Internet Browsers
- The Problem: Chrome isn't just a browser; it is a metric spy center. Furthermore, almost every other browser (Edge, Brave, Opera) runs on Google's “Chromium” engine. They're all renting space from the same landlord.
- The Solution: Firefox w/uBlock Origin (or Mull on Android via F-Droid).
Firefox is the last major holdout running its own engine (Gecko). It is the only vote you have against a total Google monopoly on how the web is rendered. uBlock Origin is non-negotiable. It blocks ads, trackers, and miners. It makes the web faster and safer.
Default Search Fix: Change your default search engine to DuckDuckGo. Google tracks your questions to build a psychological profile, DuckDuckGo just answers the question.
Run a VPN
Your ISP tracks every site you visit to build a profile. Blind them.
- The Tool: Mullvad VPN.
- The Why: Unlike Proton (which requires an email and faces Swiss legal pressure), Mullvad requires no email and accepts cash.
- The Record: When raided by authorities in 2023, Mullvad surrendered zero data, proving they truly keep no logs.
PART II: THE NEWSPAPER (RSS)
According to the Reuters Institute, “more than half (54%) of people get news from networks like Facebook, X and YouTube - overtaking TV (50%) and news sites and apps (48%)...”. It goes without saying, that social media is a bad primary news source; it's chaotic, non-chronological, and emotionally manipulated.
You need a “Newspaper”. A silent, reliable delivery of facts.
- The Tool: Feeder or Read You (via F-Droid).
- The Use Case: “I want to know what happened, when it happens, BEFORE the meme brigade hits me.”
- The Logic: RSS (Really Simple Syndication) allows you to directly subscribe to a website that supports it. You get the article the moment it is published, in a clean text format, and avoid the temptation to skip right into the comment section.
We use RSS to hold back noise.
PART III: THE TOWN SQUARE (Nora)
Reading the news in an RSS feed paints a clear, but often incomplete, picture, absent of nuance. Often, the real story isn't in the article; it's in the top comment from a local who says, "I live here, and this is what actually happened."
To lose the comment section is to lose the Context, but to install the Facebook/Reddit/X app is to welcome a spy into your bedroom.
The Solution: Nora (The SCIP container) Nora is a FOSS "Wrapper" app available on F-Droid. It's a "Clean Room" for your social media.
- The Magic: It lets you log into Reddit, Facebook, Instagram, LinkedIn, Bluesky, and X (Twitter) simultaneously inside a single app.
- Minds its business: Unlike the official apps, Nora cannot scan your contact list, check your other apps, or map your GPS history. It is just a web browser that identifies as a phone.
- Clean Feeds: It automatically strips tracking tags (
?utm_source=) and blocks "Sponsored" posts unclogging your feed.
Rules of Engagement
Do not treat social media apps as your "Homescreen." It is your window into church groups, neighborhood meetings, and family circles.
- Keep It Clean: Uninstall the official apps. They are spyware. Use Nora to keep the platform trapped in a box.
- Context Loop: When you read a breaking story in your RSS feed, use Nora to check the digital battlefield. Search for the topic. Read the dissenting opinions. The truth usually lies halfway between the Headline and the Top Comments.
- Community Defense: If you see a bot spreading blatant lies in your local group, you have a duty to correct it. Use Nora to drop the truth bomb (with a credible link), then close the app.
| Tool | Best For | Pros | Cons |
|---|---|---|---|
| Nora | General Activists | Handles FB, Insta, Reddit, X in one app. | It's a "Web Wrapper" (feels like a browser). |
| Infinity | Best native Reddit experience (FOSS). | Only does Reddit. Requires API key (Advanced). | |
| Mull + uBlock | Paranoid Activists | Maximum privacy (Hardened Firefox). | Clunky UI for social media. No notifications. |
| NewPipe | Entertainment | Watching YouTube/SoundCloud. | Read Only. You cannot comment or fight back. |
We use Nora to express our beliefs, without compromising our devices.
PART IV: RECLAIMING YOUR DESKTOP
If your computer serves you ads in the Start Menu, AI slop code that repeatedly breaks your workflow, and uses AI to screenshot your activity every few seconds, it is not your Personal Computer. It's a terminal squatted on, by Microsoft.
Since the launch of Windows 11, the mask has slipped. The boot menu has broken. The telemetry is unavoidable. The “Operating System” has become a glorified Ad Platform.
The Solution? Forced Eviction. You don't need to be a coder to jump ship, just get a USB stick and load it with any distribution of Linux.
The "Just Works" Option: Linux Mint
- For: The Windows refugee who wants their Start Button back.
- The Vibe: It looks like Windows 7. It acts like Windows 7. But it is faster, safer, and free.
- The Promise: No ads. No forced updates. No AI spyware. It respects you.
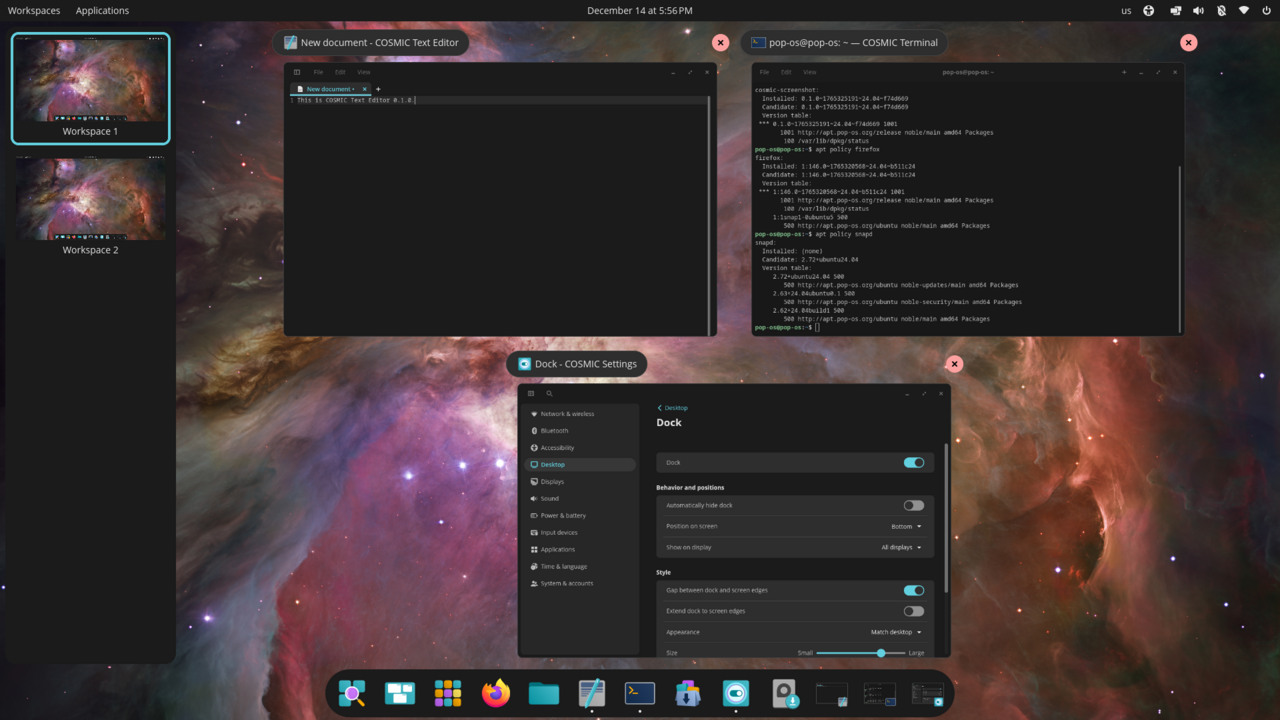
The "Power User" Option: Pop!_OS
- For: The creator, the gamer, and the programming tinkerer.
- The Vibe: Modern, slick, and designed for productivity.
- Culper's Choice: This is the OS that powers Provisional Record. It features built-in window tiling (for multitasking) and full-disk encryption out of the box.
- The Privacy: Pop!_OS makes money by selling hardware (laptops), not by selling your data. The OS itself is pure FOSS.
The Test Drive: You don't have to delete Windows today. Download the ISO file for Mint or Pop!OS. Flash it to a USB drive (using a tool like Ventoy). Plug it in and reboot. You can run the entire OS from the stick to “test drive” it without touching your hard drive (although test drives typically run slow.)
Warning: Once you experience a computer that doesn't treat you like a product, you won't want to go back.
PART V: THE ALL SEEING TV
If your television requires an internet connection to function, it's not a screen; it's a Telescreen-lite.
Through a technology called ACR (Automatic Content Recognition), modern TVs scan every pixel on your screen to build a profile of your politics, habits, and health. This includes a DVD player, or any other device connected to your TV.
1. The Hardware Rollback
The most effective privacy option in this regard, is a "non-smart" TV.
- Top of the Line: “Non-smart” TVs are still produced, they've just mostly been de-shelved. Look online for Commercial Displays (made for hotels/signage); you want something that explicitly has no Wi-Fi or Bluetooth Connectivity, so this will generally be marked “economy”, or “essential”.
- The Thrift Option: Plainly put, a 2015-era 1080p "dumb" TV from a thrift store is more secure than a $2,000 OLED from 2026.
Why? Without the hardware to send a signal out of your TV, it becomes physically impossible to peek on your offline activity.
2. The Hostile Network (Containment)
If you must use a streaming stick or a Smart TV, treat it like a biological hazard.
- The Tactic: Never connect these devices to your primary home Wi-Fi. Create a separate "Guest Network" specifically for "Hostile Devices" like Roku or Fire Sticks.
- The Kill Switch: Ensure "Client Isolation" is enabled in your router settings. This allows the device to reach the internet (to stream Netflix), but prevents it from "seeing" or communicating with your phones, laptops, or file servers. It keeps the informant from fingerprinting other devices via device discovery.
3. The Lobotomy (Software Disconnect)
If you already own a smart TV and cannot replace it, you must revoke permissions as you can.
- Go into the settings and hunt for terms like "ACR," "Viewing Data," "Live Plus" (LG), or "Samba TV" (Sony). Turn them OFF.
- The Guide: Manufacturers hide these settings deep in the menus. I recommend following the Consumer Report's Guide to Disabling Smart TV Snooping to find the exact toggle for your model.
PART VI: THE OFFLINE ARCADE
Sovereign Play & The Co-Pilot Strategy
Modern gaming is designed to prey on children (and you). It uses “Loot Boxes,” “Daily Login Bonuses,” and FOMO to turn play into an addiction. The solution isn't to ban games; it's to fall back to the era before the casino moved in.
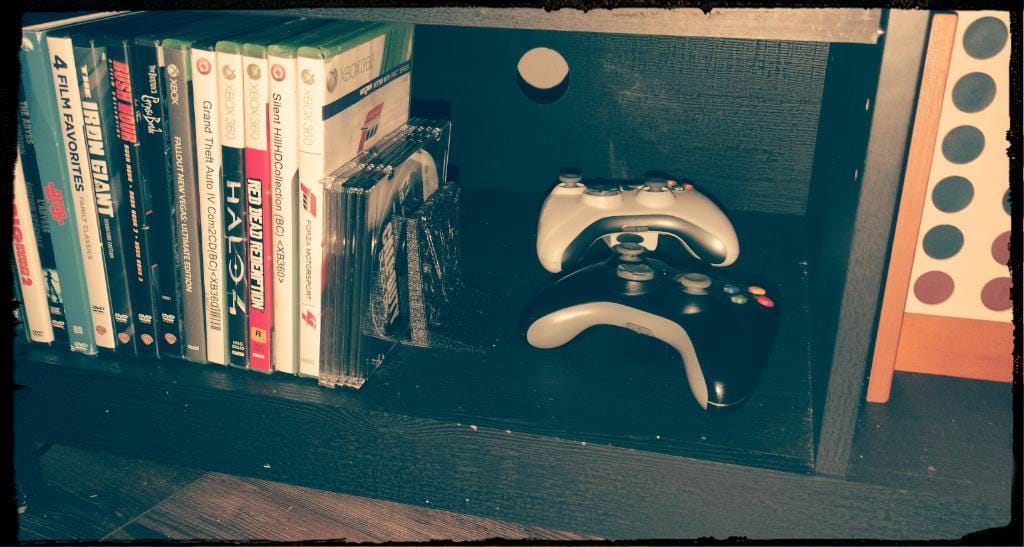
The Hardware: The Gen 7 Sweet Spot (Xbox 360 / PS3)
- Ownership: You own the physical disc; Microsoft cannot delete Skyrim or GTA:V from your actual shelf.
- Privacy: An Xbox 360 does not need an internet connection. It's a closed loop. No telemetry, no voice listening, no psychological profiling.
- Cost: You can build a library of 50 masterpieces for the price of two modern PS5 games.
The "Co-Piloting" Strategy (Parenting Win)
Don't just hand the kid a tablet. Sit on the couch.
- Proxy Gaming: Having your kid play skyrim while you watch, is safer than letting them play Fortnite alone. You are the curator. You guide them through the moral gray areas: “Why should we help that stranger? Is the treatment of dark elves in Windhelm, okay? Does Paarthurnax deserve punishment?”
- Couch Co-Op Revival: Modern games isolate you. Old-school games were made to play together!
The Result: You're high-fiving in real life, spending time with your kids and reliving your childhood; just think of all the games you wouldn't replay alone.
- Marvel: Ultimate Alliance
- Splinter Cell: Double Agent
- Army of Two
- Forza Horizon (1)
- The golden generation of Call of Duty
Quick Tips: Buy the discs used at flea markets, local shops, or online shops (like LukieGames) to save money and the environment. Update the games via ethernet once, then keep the console OFFLINE. It's an air-gapped entertainment machine, since even the units with Wi-Fi struggle to connect to modern modems.
Even if the internet goes down, the fun continues!
PART VII: A SOVEREIGN SOUNDTRACK
Plainly, your music should not profile you. It should not track your location. It should not serve you ads.
- The Hardware Path: iPod Classic (5.5 or 7th Gen) running Rockbox.
- Why: It is school-safe, disconnect-friendly, and built like a tank. It plays music. That’s it.
- The Software Path: RiMusic (via F-Droid).AntennaPod: Takes over for Spotify specifically for podcasts.
- Why: Hits like Spotify, but utilizes YouTube Music for audio. Strips the ads and tracking, allows offline caching; respects your privacy. Saves you a subscription, allows you stream music and create playlists.
Advanced users may enjoy Metrolist from Github (also only for music).
THE VERDICT
You do not have to live in a cave to escape the dragnet. You just have to be intentional.
- Get your tools from F-Droid.
- Get your news from RSS.
- Get your browsing done with Firefox+Ublock.
- Get your community from Nora.
- Get your work done on Linux.
- Get your entertainment from Physical Disks!
If you find use in FOSS tools and apps, please seriously consider donating to them directly via their respective channels. By their very nature, just like this website, FOSS tools are often passion projects that are self, or crowd funded. In order to have a chance at retaining the freedom to express one's self, we must be able to trust that the tools we use will not betray us.
Their work is needed now, more than ever before; we must vote with our wallets.
TECHNICAL DISCLAIMER & LIABILITY WAIVER
1. Educational Purpose Only Pursuant to Section 3.B of the Provisional Record Terms of Use, the software recommendations contained in this protocol (including F-Droid, Nora, Pop!_OS, and all others) are provided solely for educational and journalistic purposes. This content does not constitute professional IT security advice, enterprise deployment guidance, or a manufacturer-endorsed instruction manual.
2. "As-Is" No-Warranty Provision The Publisher provides NO WARRANTY regarding the safety, stability, or legality of the third-party software discussed. These tools are Free and Open Source Software (FOSS) maintained by independent communities. Provisional Record has no control over, and assumes no liability for, updates, code changes, or vulnerabilities introduced by the developers of these tools after the date of publication.
3. Assumption of Risk (Data & Hardware) By choosing to install custom operating systems (e.g., Linux) or sideload applications (e.g., F-Droid), the user acknowledges and assumes all associated risks, including but not limited to:
- Data Loss: The potential corruption of files during OS installation.
- Hardware Compatibility: The risk of "bricking" or voiding manufacturer warranties on devices.
- Security Posture: The user is solely responsible for their own threat model and security configuration.
ALWAYS BACK UP YOUR DATA BEFORE ATTEMPTING ANY SOFTWARE MIGRATION.
4. Financial Independence Provisional Record accepts no financial compensation, affiliate commissions, or "kickbacks" from the projects listed in this guide. Recommendations are based exclusively on the author’s independent testing and the FOSS philosophy of user sovereignty.
5. Governance This disclaimer is a supplement to the master Terms of Use.
**Large Section added 2/11/26. For the original, please search the Wayback Machine. https://web.archive.org/

